Application Fraud — Establishing Your Fraud Risk Appetite
Fraud and security are a top priority for financial institutions — but just stopping fraud isn’t enough. Managing fraud is a balancing act that starts with knowing your fraud risk…

In my previous post on application fraud, we explored the drivers behind the rapid acceleration of identity-based fraud, which includes identity theft / third-party fraud, synthetic identity fraud, and first-party fraud. Fraud and security are a top priority for financial institutions — but just stopping fraud isn’t enough. Managing fraud is a balancing act that starts with knowing your fraud risk appetite.
Fraud managers have to look beyond losses and loss prevention and consider consumers’ need for a frictionless experience, regulators’ stipulations and the competitive pressures of fintech disruptors. Fraud managers need to ask:
- How do we keep current customers satisfied that we adequately protect them, but don’t inconvenience them by declining legitimate transactions?
- How do we keep our fraud controls relevant, agile, and modern to accommodate new products, new channels, increased digitization and more faceless interactions?
- How do we facilitate growth of the business and new customer acquisition?
- How do we leverage the greatest in advanced analytical fraud detection methodology such as machine learning and artificial intelligence while maintaining the transparency mandated by regulators?
Step 1 – Balancing Act
Step 1 in setting your fraud risk appetite requires balancing 3 key levers: Detection Rate, Review Rate, and False Positive Rate. For example, finding 95% of your frauds in the top 3% of risk-ranked referrals with a 20:1 false positive rate. The majority of fraud managers are intimately familiar with establishing this process for each of their controls, e.g., X is my threshold for application fraud, Y is my threshold for card fraud, Z is my threshold for wire fraud.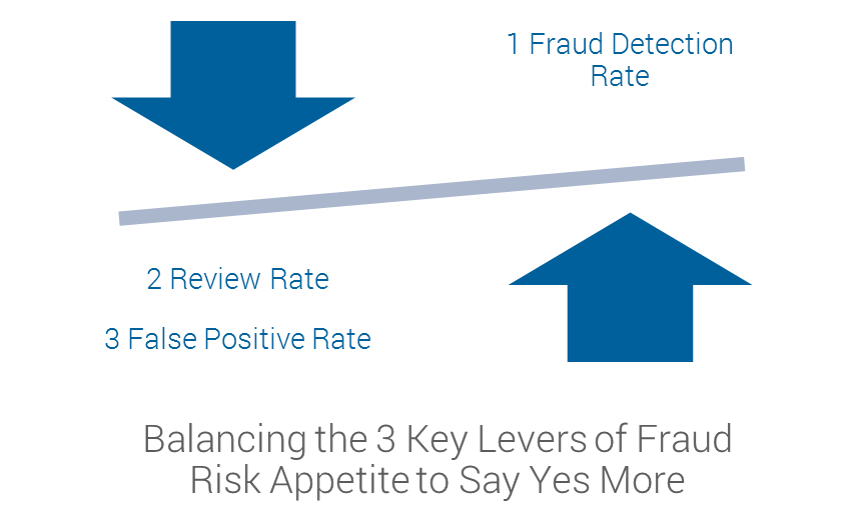
Step 2 – Identity Proofing and Information Sharing
Step 2 begins with recognizing that the thresholds of “Yes-Fraud” “No-Not Fraud” aren’t black and white, and shouldn’t be viewed in isolation. There is a “Maybe” answer that says “Maybe this person is an application fraud. I’m not ready to turn them down as a customer, but maybe I should be treating their transactions a bit differently than someone who is definitely not fraud.”This concept speaks to the idea of protecting your organization across the customer lifecycle. At point of origination, you stop the obvious frauds. The maybe frauds and the not frauds, they become customers because you are trying to grow your business. But what if we take what we learned about these customers at point of origination and we carry it through to our downstream controls?
What if we constantly iterate across our customer base to understand how a customer’s identity risk changes over time given the introduction of new data – how they transact, what device they use to log in to an account, what new applicants or customers share information with them? In order words, identity proofing doesn’t stop just because an applicant became a customer. New information means new intelligence that we can act on.
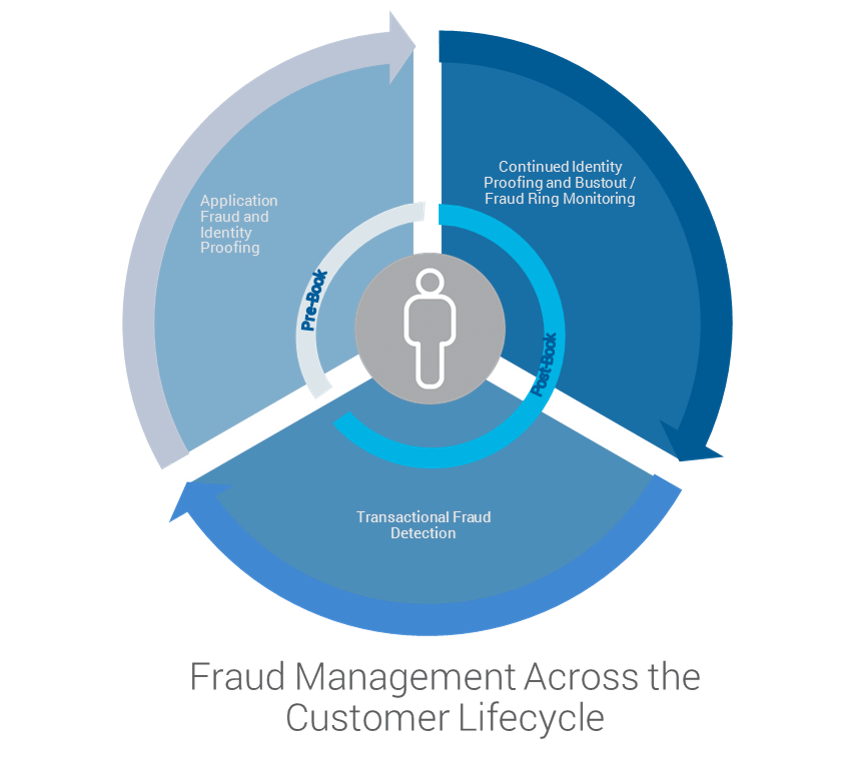
And looking further down the customer lifecycle, what if we use this intelligence to improve how we detect transactional fraud, including non-monetary transactions that may indicate an account takeover (ATO) or financial transactions that indicate payments fraud?
If an applicant has a medium risk of synthetic identity fraud at point of origination, this risk assessment may increase over the course of several years as new data indicates the now customer is part of a fraud ring. What if your organization can act on that identity now? Or, what if your organization can now better segment transactional fraud controls that detect bust-out transactions?
The concept of protecting across the customer lifecycle should not just be about sharing intelligence downstream, but also thinking about a bilateral sharing of intelligence – what you learn in your transactional fraud detection, what you learn in ATO root cause analysis, is intelligence that can be brought forward into your application fraud controls.
Step 3 – Collaboration with Risk
Lastly, step 3 requires thinking big across the risk and the fraud continuum. As discussed in a recent blog post, collections strategies are oftentimes wasted on fraud that is masquerading as bad debt. Recognizing there can be a fuzzy line between credit risk and fraud, means also recognizing the risk and fraud controls have room to interplay and benefit each other.Taking the paradigm of protecting across the customer lifecycle, and merging it with a similar assessment of an organization’s risk controls, we experience significant gains. For example, while the capabilities to detect fraud and assess risk at point of origination may differ, the data ecosystem has huge overlaps.
In a similar vein, risk controls in customer management that manage credit line increases, payments clearances, etc., can improve fraud detection when they have intelligence about a customer’s evolving fraud risk and use this intelligence to segment treatments. Lastly, a collections practice is optimized operationally, financially and analytically when we are able to determine which accounts are fraudulent (no intent to pay) and which are legitimate bad debt (limited ability to pay).

The Fraud and Risk Continuum
Setting a fraud risk appetite is about creating a balance for your business and recognizing that there is more to assess than just losses. If we starting thinking across the customer lifecycle, across the fraud and risk continuum, we can strengthen our defenses, find synergies in data, technology, and analytics, and take a big step forward in top line growth, profitability, compliance, and protecting the bottom line.In my next post I will take a more technical nose-dive to understand the convergence of fraud and security. What does the dark web have to do with application fraud?
Feedback is welcome and I look forward to sharing with you more.
Popular Posts

Has the Reporting of Rental Data to the Credit Reporting Agencies (CRAs) Increased?
FICO Score 10T includes rental data, but consumers can only experience the benefit of this to the extent that their rental data is reported to the CRAs
Read more
Average U.S. FICO® Score at 716, Indicating Improvement in Consumer Credit Behaviors Despite Pandemic
The FICO Score is a broad-based, independent standard measure of credit risk
Read more
FICO Statement on FHFA and FHA Updates to Credit Score Modernization
FICO supports FHFA’s announcement that the long-anticipated historical data for FICO® Score 10T will be released to the mortgage market.
Read moreTake the next step
Connect with FICO for answers to all your product and solution questions. Interested in becoming a business partner? Contact us to learn more. We look forward to hearing from you.
