What Is Telecom Subscription Fraud?
Subscription fraud occurs when a fraudster uses their own, a stolen or a synthetic identity to obtain mobile devices and services with no intention to pay.

Fraud is a serious concern for the communications industry, with proceeds and services used by organised crime and terrorist networks. Whilst reliable statistics are difficult to come by, industry association Communications Fraud Control Association estimates the total global fraud loss at around $29 billion annually, according to a CFCA 2017 Global Fraud Loss Survey. Of this, over $7 billion is attributed to subscription fraud and account takeover.
In an industry which is undergoing widespread digital transformation to streamline customer journeys and reduce operating costs through automation, there are clear implications and requirements to prevent fraud.
Defining Subscription Fraud
Subscription fraud occurs when a fraudster uses their own, a stolen or a synthetic identity to obtain mobile devices and services with no intention to pay. As the wholesale, and retail, purchase cost of devices has increased over recent years, a grey market has been created and exploited by fraudsters obtaining devices to resell for lucrative profits. The mobile device subsidy model that is still prevalent across most of Europe, whereby customers have little to no outlay upfront and receive an expensive device that can be resold, lends itself to a high-margin business model for the unscrupulous.
There are numerous other drivers for subscription fraud, including;
- A proliferation of digital identity information. The ‘want it now’ culture of today’s consumer means that the technologies we all love to use for their convenience make it easier for fraudsters to do what they do, e.g., bots designed to test login credentials or to generate customer orders using stolen or synthetic identities.
- An increasing amount of data breaches across all industries. This results in organised fraudsters sitting on customer information until they decide to use it.
- A ‘convergence’ of fraud. As many services now employ the smart phone as a contact point for verification, such as a One Time Passcode via SMS. The consumer’s mobile account has become fundamental as part of an authentication trail in many services such as banking. Fraudsters therefore target customers’ accounts in order not to defraud just the telecoms company but the customer themselves in order to manipulate their financial, or other services.
First-Party Subscription Fraud
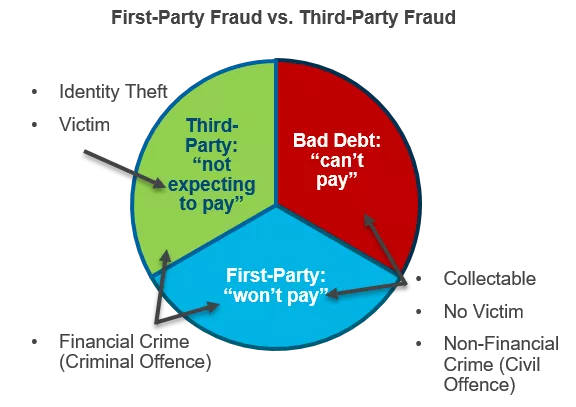
Solutions that offer identity verification and validation services are unable to address the critical question of first-party fraud — those customers that own the identity but have no intention to pay for the services or devices. And the question of intent can vex credit assessment and identity fraud systems. First-party subscription fraud looks like a credit risk issue of delinquency / default. A large proportion of fraud may be classified as bad debt which also has consequences on resource-stretched collections operations. If the company is trying to collect a debt where there is no intention to pay then it’s a waste of resource as well as a potential opportunity cost.
The first-party fraud also includes a significant proportion of ‘mules’, with university students often targeted. They are instructed to apply for as many devices as they can in return for the promise of quick cash. Often, the mule doesn’t consider the impact this will have on their future credit rating, or maybe they don’t care, as is the case with some foreign students taking out devices shortly before returning overseas and leaving the debt behind them.
Source: FICO Blog
And of course, once a subscription is activated and in the hands of an organised fraudster, the subscription fraud can then be the forerunner to commit other types of telecoms fraud, such as interconnect bypass and international revenue share fraud.
Recognising Intent to Pay
It’s obviously better to prevent the fraudulent contract being taken out in the first place rather than pick it up through network traffic monitoring. By that point a chunk of the damage is already done and, if there was a device provided, it is now a financial loss.
Whilst it’s easy to point out the obvious and that CSPs could be preventing subscription fraud at the point of sale, the reality is much more difficult. As mentioned above, being able to identify the intent to pay isn’t easy. Couple this with onboarding and upgrade processes that are designed to minimise friction in the customer process, and fraud teams need to be sophisticated in how they identify subscription fraud without impacting the customer journey for the genuine customers.
There are a number of different types of fraud modus operandi to contend with too, from organised gangs, to opportunists tempted to take advantage of poor process or loopholes, to ‘sleeper’ fraudsters who bide their time before conducting fraudulent activity, to ‘hit and run’ fraud that is aggressive in terms of speed and value stolen.
In my next post, I’ll discuss account takeover fraud, and then how to tackle these kinds of fraud.
For more information, see our white paper on Fraud in the Digital Experience Era – Telecommunications.
Popular Posts

Has the Reporting of Rental Data to the Credit Reporting Agencies (CRAs) Increased?
FICO Score 10T includes rental data, but consumers can only experience the benefit of this to the extent that their rental data is reported to the CRAs
Read more
Average U.S. FICO® Score at 716, Indicating Improvement in Consumer Credit Behaviors Despite Pandemic
The FICO Score is a broad-based, independent standard measure of credit risk
Read more
FICO Statement on FHFA and FHA Updates to Credit Score Modernization
FICO supports FHFA’s announcement that the long-anticipated historical data for FICO® Score 10T will be released to the mortgage market.
Read moreTake the next step
Connect with FICO for answers to all your product and solution questions. Interested in becoming a business partner? Contact us to learn more. We look forward to hearing from you.
