Top 5 Fraud & Security Posts: AI Meets AML (and Hackers)
One of the newer applications of artificial intelligence rose to the top of the Fraud & Security blog last year: anti-money laundering. Readers were also keenly interested in learn…

One of the newer applications of artificial intelligence rose to the top of the Fraud & Security blog last year: anti-money laundering. Readers were also keenly interested in learning more about cybersecurity and ATM compromise trends.
Here were the top 5 posts of 2017 in the Fraud & Security category:
AI Meets AML: How the Analytics Work
AI Meets AML: How Smart Analytics Fight Money Laundering

As FICO began using AI to detect money laundering patterns, three of our business leaders blogged about why and how AI was being applied. Two of the top posts of the year related to this topic, with TJ Horan explaining why advanced analytics are needed. He noted three ways AI systems improve on traditional AML solutions:
- More effective than rules-based systems: “As regulations become ever more demanding, the rules-based systems grow more and more complex with hundreds of rules driving know your customer (KYC) activity and Suspicious Activity Report (SAR) filing. As more rules get added, more and more cases get flagged for investigation while false positive rates keep increasing. Sophisticated criminals learn how to work around the transaction monitoring rules, avoiding known suspicious patterns of behavior.”
- Powerful customer segmentation: “Traditional AML solutions resort to hard segmentation of customers based on the KYC data or sequence of behavior patterns. FICO’s approach recognizes that customers are too complex to be assigned to hard-and-fast segments, and need to be monitored continuously for anomalous behavior.”
- Rank-ordering of AML alarms: “Using machine learning technology, FICO has also created an AML Threat Score that prioritizes investigation queues for SARs, leveraging behavioral analytics capability from Falcon Fraud Manager. This is a significant improvement, since finding true money-laundering behavior among tens of thousands of SARs is a true needle-in-the-haystack analogy.”
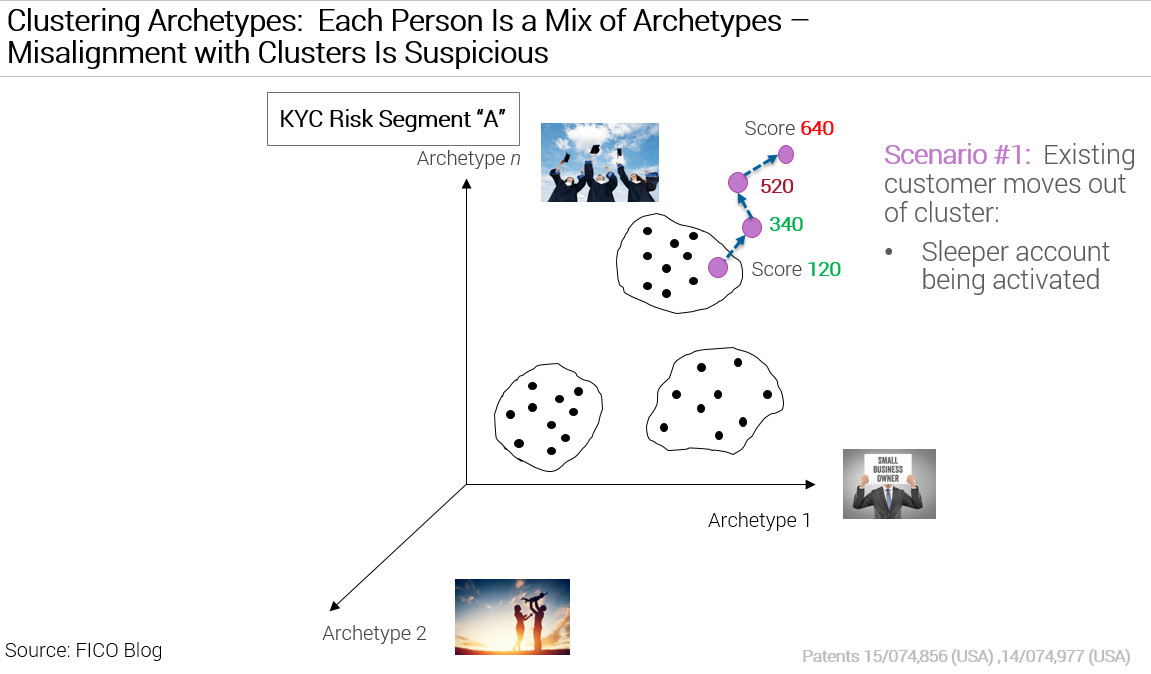
FICO Chief Analytics Officer Dr. Scott Zoldi followed up by explaining two techniques FICO has applied to AML, soft clustering and behavior-sorted lists. Of the first, he wrote:
“Using a generative model based on an unsupervised Bayesian learning technique, we take customers’ banking transactions in aggregate and generate “archetypes” of customer behavior. Each customer is a mixture of these archetypes and in real time these archetypes are adjusted with financial and non-financial activity of customers. We find that using clustering techniques based on the customer’s archetypes allows customer clusters to be formed within their KYC hard segmentation.”
What Is a Cybersecurity Posture?
The latest trend in cybersecurity is enterprise security ratings that benchmark a firm’s cybersecurity posture over time, and also against other organizations. Sarah Rutherford explained exactly what these scores measure.
“The cybersecurity posture of an organisation refers to its overall cybersecurity strength,” she wrote. “This expresses the relative security of your IT estate, particularly as it relates to the internet and its vulnerability to outside threats.
“Hardware and software, and how they are managed through policies, procedures or controls, are part of cybersecurity and can be referred to individually as such. Referring to any of these aspects individually is talking about cybersecurity, but to understand the likelihood of a breach a more holistic approach must be taken and an understanding of the cybersecurity posture developed. This includes not only the state of the IT infrastructure, but also the state of practices, processes, and human behaviours. These are harder to measure, but can be reliably inferred from observation.”

Hacked ATMs Lead to 70% Rise in Debit Card Fraud

2017 saw a continued increase in compromised ATMs in the US. As TJ Horan reported:
- The number of payment cards compromised at U.S. ATMs and merchants monitored rose 70 percent in 2016.
- The number of hacked card readers at U.S. ATMs, restaurants and merchants rose 30 percent in 2016. This new data follows a 546 percent increase in compromised ATMs from 2014 to 2015.
TJ also provided tips for consumers using ATMs.
Why Do Hackers Commit Cyber-Attacks?
With all the focus on data breaches, Sarah Rutherford posed this question, and provided the top three reasons:
- For financial gain
- To make a political or social point
- For the intellectual challenge
“The ‘why’ of cybercrime is complex,” she added. “In addition to the motivations already mentioned, hackers could also be motivated by revenge or wish to spy to gain commercial or political advantage. The different motivational factors for hacking can coincide; a hacker who is looking for an intellectual challenge may be happy to also use their interest to make money or advance their political agenda.”
Follow this blog for our 2018 insights into fraud, financial crime and cybersecurity.
Popular Posts

Has the Reporting of Rental Data to the Credit Reporting Agencies (CRAs) Increased?
FICO Score 10T includes rental data, but consumers can only experience the benefit of this to the extent that their rental data is reported to the CRAs
Read more
Average U.S. FICO® Score at 716, Indicating Improvement in Consumer Credit Behaviors Despite Pandemic
The FICO Score is a broad-based, independent standard measure of credit risk
Read more
FICO Statement on FHFA and FHA Updates to Credit Score Modernization
FICO supports FHFA’s announcement that the long-anticipated historical data for FICO® Score 10T will be released to the mortgage market.
Read moreTake the next step
Connect with FICO for answers to all your product and solution questions. Interested in becoming a business partner? Contact us to learn more. We look forward to hearing from you.
