Top 5 Fraud and Financial Crime Topics of 2021
Our most popular fraud and financial crime posts explored trade-based money laundering, non-fungible tokens, buy now pay later scams, courier scams and good old credit card fraud

From TBML to BNPL to NFTs, 2021 found fraud and financial crime professionals dealing with a plethora of new challenges and criminal schemes. Our five most popular posts of the year dealt with trade-based money laundering, non-fungible tokens, buy now pay later scams, courier scams and good old credit card fraud. Here are excerpts.
TBML: What Is Trade-Based Money Laundering?
Trade-based money laundering (TBML) is a growing risk, as seemingly legitimate transactions are exploited by criminal groups to launder funds and finance terrorist activity. In its simplest definition, trade-based money laundering is the process of disguising the proceeds of crime and moving value (i.e., movement of money) using trade transactions to legitimize their illicit origins. TBML involves the exploitation of the international trade system for the purpose of transferring value and obscuring the true origins of illicit wealth. TBML schemes vary in complexity but typically involve misrepresentation of the price, quantity, or quality of imports or exports.
Typical TBML common techniques include:
- False reporting on invoices, such as commodity misclassification, commodity over- or under-valuation.
- Repeated importation and exportation of the same high-value commodity, known as carousel transactions.
- Commodities being traded that do not match the business involved.
- The over- or under-valuation of goods on the invoice and other documentation.
- Over- or under-shipment of goods or services (also, phantom shipments).
- Shell companies or offshore front companies.
- Third-party intermediaries facilitating invoice settlement.
- Illicit cash integration in financial settlement.
- Misuse of existing trade chain to move funds for terrorists (evasion of sanctions / financing of terrorism).
Read the full post: TBML: What Is Trade-Based Money Laundering?
NFTs and Money Laundering - Are Fraudsters Becoming Artists?
Erik Stretz wrote: I think NFTs are even better for illicit purposes than traditional art, simply because the hurdles are lower. When we move to the world of digital art and NFTs, the provenance and authorship of the works of art are obscure to say the least. And yet they are exchanging hands for huge sums, making them a great vehicle for money launderers. So, how do criminals go about using NFTs to launder money?
Four steps to using NFTs for money laundering:
- Create the artwork. A single grey pixel sold for ~$1.4 million. The grey box at the top of the linked article is not a picture failing to load – it’s the artwork! Meanwhile these low-pixel 24x24 images of ‘punky-looking guys and girls’ (CryptoPunks) are according to their creators the first NFTs. They are generated algorithmically and they’re selling for millions of dollars – even though there’s no human artist involved in creating them beyond programming the algorithms. At the risk of sounding disdainful about these purported works of art, fraudsters can create similar works by programming the required algorithms without too much trouble (are they even fraudsters in this scenario, or actually artists?).
- Create the artist. Identity fraud is easier than ever thanks to the digital world we are living in. Fraudsters can steal identities, or artificially create them. It takes a little work, but with more and more services being digital, it’s not that hard to fake an identity, and to give it a life on Facebook, Instagram or with a few well-placed credit applications even in ‘real life’. Fraudsters can create months and years’ worth of identities that are completely made up. By using bots to create digital art and ascribing them to a fake identity that hides behind a nickname, you can achieve nearly peak anonymity.
- Create a web presence, using servers in jurisdictions that do not cooperate with international policing efforts.
- Trade your digital artwork (aka NFTs) using crypto currencies.
These four steps may seem a hypothetical scenario, but it is relatively simple and a tempting proposition for anyone looking to launder money. With art that is purely digital and can be created anywhere, there is no need for shipping, and nobody needs to put their hands on it. We have artists that might only be active via digital channels and thus have a purely digital identity. If there is nothing to show physically, you have even less reason to be anywhere in person. Such art is primarily traded on digital platforms using crypto currency, making tracking and controlling the trade and the vast sums of money behind it even more opaque.
Read the full post: NFTs and Money Laundering - Are Fraudsters Becoming Artists?
BNPL Fraud — When "Buy Now, Pay Later" Backfires
Darryl Knopp wrote: For banks with their own BNPL offering, a multi-layered approach to risk management and fraud protection is critical. The first step is to address BNPL fraud strategically by establishing an explicit understanding of the bank’s risk appetite for this offering—what is the tolerance level for customer offer/acceptance versus fraud risk? Going a layer deeper, that includes clear differentiation between BNPL bad debt and first-party or synthetic fraud and abuse. This extends to an operational level, at which account-based operations are segmented from transaction-based monitoring; if first-party fraud is suspected, it must be addressed separately from standard third-party suspicious fraud transaction verification queues.
BNPL fraud presents yet another powerful incentive to implement enterprise fraud defenses. As my colleague Matt Cox recently blogged, an enterprise fraud approach delivers a composite view of a customer’s inflow and outflow activity by breaking down traditional silos of credit, debit, deposits and payments (person-to-person, mobile, wire transfers, ACH and more), adding application fraud detection to that view. In this way, banks can assess the totality of customer behaviors to better flag potentially fraudulent BNPL loans applications at the point of sale, denying the credit request before the fraudster walks off with the merchandise. Furthermore, link analysis plays an important role in the application process, ensuring there are no ties or known correlation between applicants and organized fraud rings or prior fraud cases.
Banks can deploy additional sophisticated technology measures to reduce card fraud. They can implement well thought-out customer journeys that include robust identity proofing and verification during customer account onboarding, especially through digital channels. In the absence of a hard credit inquiry, smart orchestration of external intelligence is necessary — device telemetry, behavioral analytics, telephony and contact intelligence all can indicate the likelihood of fraud without creating undue friction. Machine learning models provide the analytic horsepower to assess all purchases/transactions in real-time, correlate that data with the ID proofing, authentication and customer behavior data.
In sum, BNPL fraud presents a new fraud challenge for banks— in certain instances it’s essentially an instant loan application, at the point of sale, without the benefit of a credit check.
Read the full post: BNPL Fraud — When "Buy Now, Pay Later" Backfires
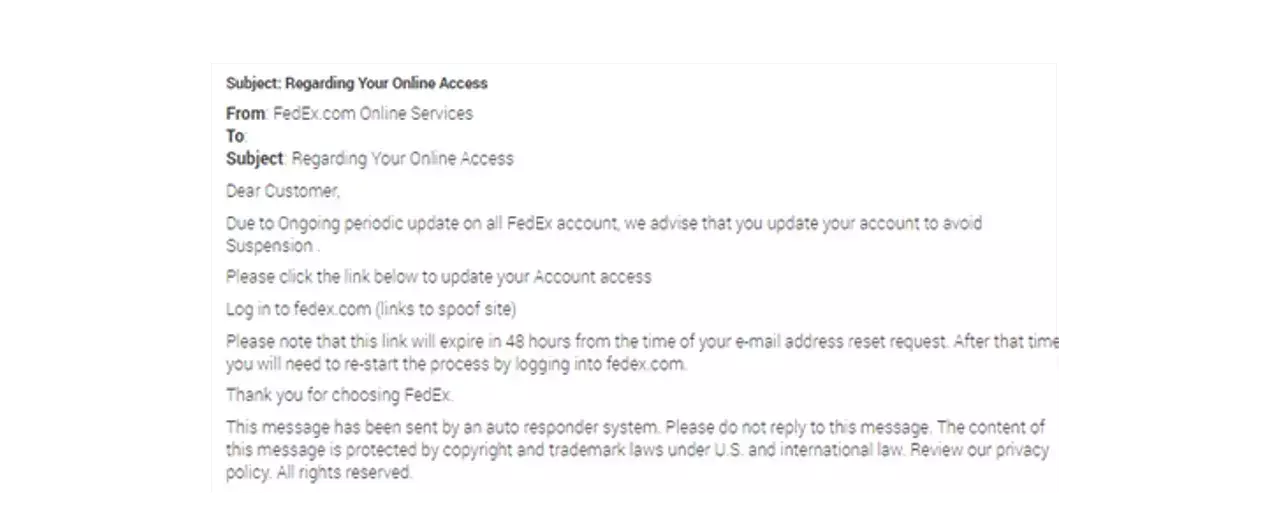
Courier Scams – How They Work And How To Fight Them
Toby Carlin wrote: The attack is simple – an SMS or email comes out of the blue from an unknown number or address, notifying the target that they have missed a delivery and that it will need to be re-arranged. These typically reference the largest of the local delivery companies or even the central mailing services within the attack region. When the victim follows the link to re-arrange their fake delivery, they are asked for a host of information along with a fee for redelivery. These scams are very successful — here’s how they work:
1. A fraudster will always imitate a company to generate maximum potential to find a victim. This is why tax entities and home utilities are always a popular target for fraudsters, but during COVID-19 lockdowns, our lives were forced to be remote – which brought with it an increase in the use of courier services to meet the exploding demand of customers purchasing from e-commerce channels. Mix this increase in consumer demand with the fact that most customers purchase from a vendor they know, but they do not know who will be delivering the item, and you have a rich and varied target set for the fraudster.
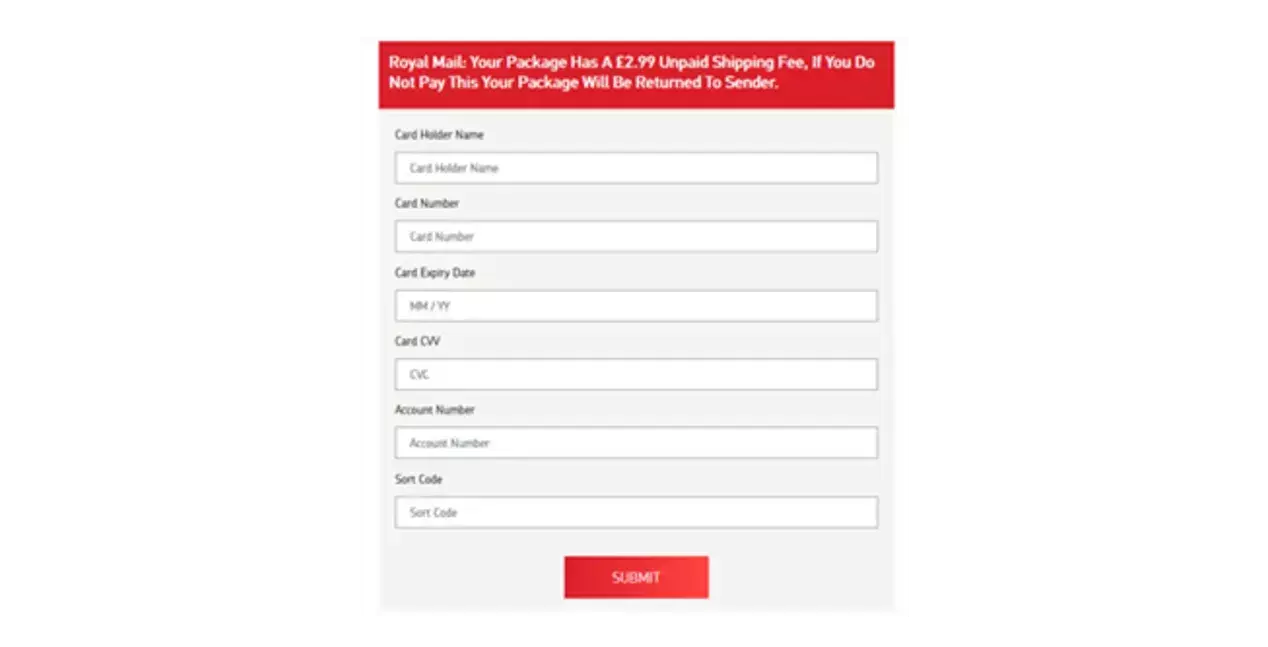
2. Like many modern card and e-commerce frauds, the scam itself contains a range of attack vectors in a single place. This includes phishing of personal and account-level information as well as compromising the PAN / CVV for use in a fast-following fraud attack. It is also becoming more common that these attacks are part of a unified scam whereby high-value fraudulent goods are being ordered in the background, with the customer then tricked into completing the authentication steps prompted by their ‘redelivery’.
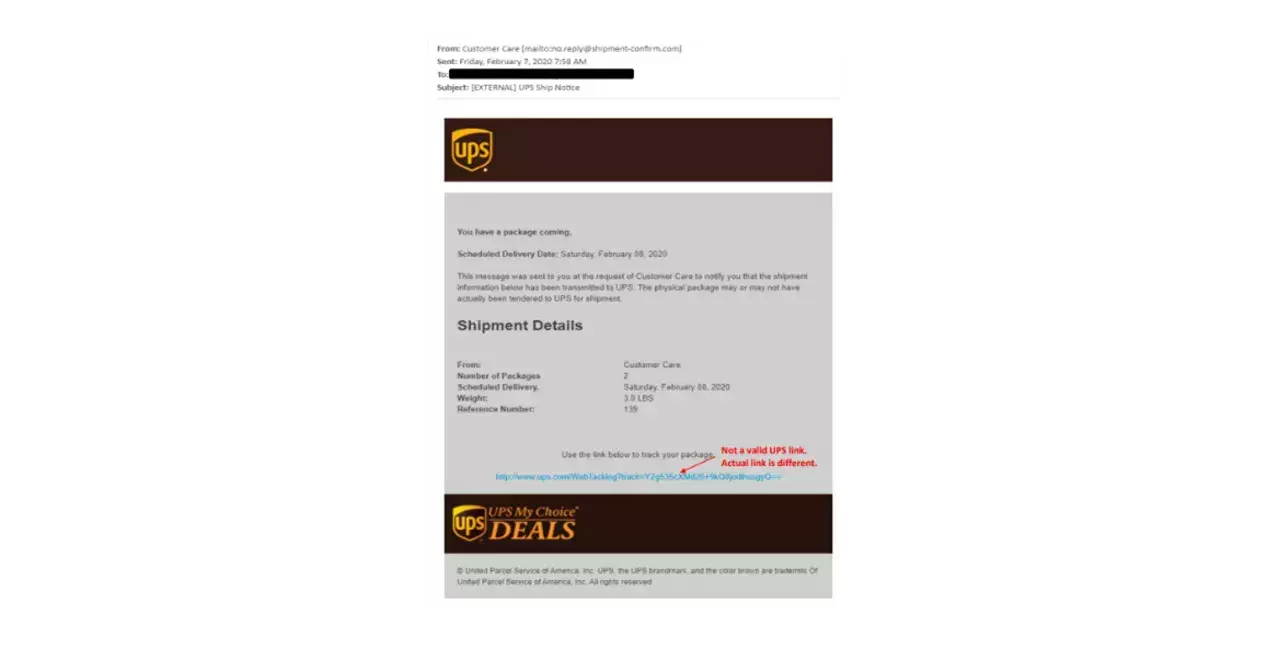
3. Creating a multi-layered and extremely convincing web page to mimic genuine services is easier than ever before. Mass communication methods by SMS or email are commonplace and often incredibly low cost – a service that is enjoyed by fraudsters and genuine companies alike. It is also quicker and easier than ever to purchase and design a high-quality web domain and even more troublesome is that in many instances, the design includes an offering for fraudulent mobile applications. All of these schemes are low-cost, but highly effective.
How to Fight Back
To get ahead of these attacks, we must encourage more reporting and better collaboration in the fight against such frauds along with continuing to strengthen controls around data compromise detection which forms the basis of targeting these threats. As with all types of fraud, combining intelligence and fraud prevention efforts will always win out against the fraudster. This approach has underpinned the best-in-class performance of FICO for over 30 years.
FICO is investing heavily in the global fight against fraud scams. This week we launched the first analytic models to profile and identify scams, built on the global community of Falcon Fraud Manager customers, the FICO Falcon Intelligence Network. This is the first model of its kind globally and represents an exciting development in beating back the ever-increasing threat of cross-channel scams.
Your customers must be warned and given the appropriate routes in which to easily report such scams to ensure enforcement activity happens quicker. Services such as Action Fraud in the UK, the Better Business Bureau (BBB) in the US and each individual delivery company are great example of such reporting.
But it is also incumbent on the banks to do more to remove silos and offer a more complete and holistic view of emerging fraud across their entire enterprise. Taking advantage of consortium data sets for all fraud types and scams is also essential to deal with this modern threat.
Read the full post: Courier Scams – How They Work And How To Fight Them
Credit Card Fraud: It’s Still A Thing (And As Big As Ever)
TJ Horan wrote: Exactly how big credit card fraud is depends on where you look. The U.S. Federal Trade Commission (FTC) is an important resource, taking in reports from consumers about problems they experience in the marketplace. The reports are stored in the Consumer Sentinel Network (Sentinel), a secure online database available only to law enforcement partners, which can use information in the database to spot trends, identify questionable business practices and targets, and enforce the law.
The graphs below show the top fraud types reported to the FTC in 2019 and corresponding dollar loss amounts.
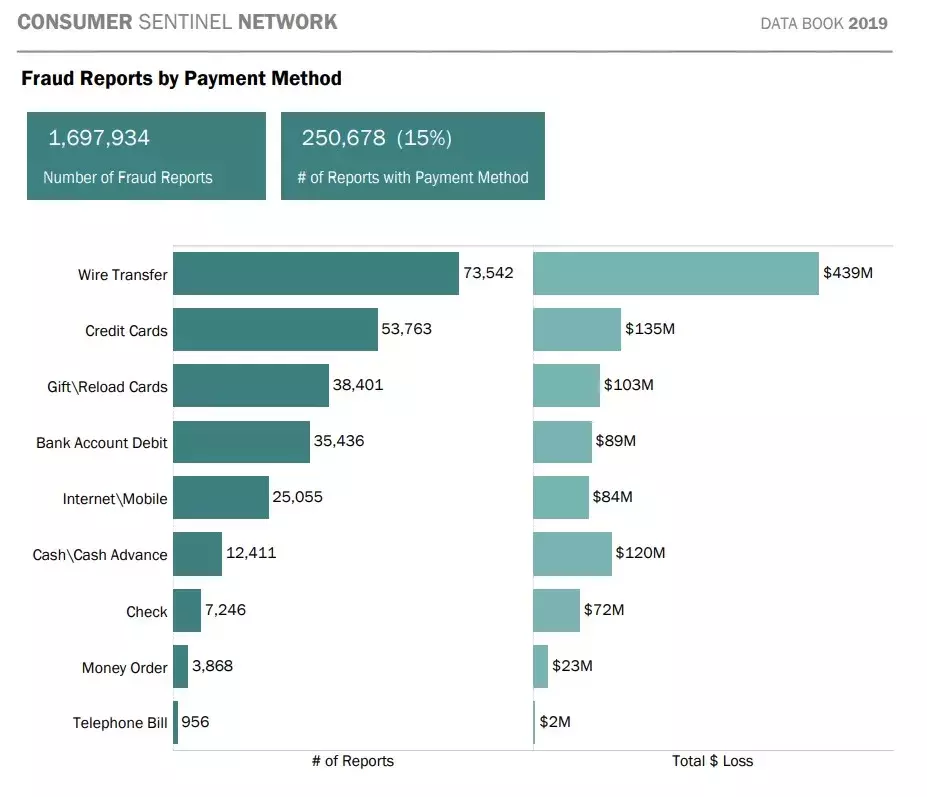
Credit card fraud was the FTC’s second most-reported fraud type in 2019. It’s important to note that the numbers in the graph above reflect only the total 250,678 incidents reported to the FTC; a much higher number of credit card fraud incidents impact banks and issuers. The important point here is that’s the second largest type of fraud reported to the FTC by consumers, indicating it’s still a large problem and causing pain to the victims.
For example, in April 2020, early in the pandemic, The Wall Street Journal reported that fraud losses – including losses linked to credit and debit cards – cost banks, merchants and, in some cases, cardholders $16.9 billion in 2019, according to Javelin Research. Note the dramatically higher number here; $16.9 billion is more than 125 times greater than the $135 million, credit card-only figure from the Sentinel report.
Additionally, payment services provider FIS (a FICO Partner) said the dollar volume of attempted fraudulent transactions in April 2020 rose 35% over the prior year, a trend it expected to continue.
More recently, in December the Nilson Report quantified global card fraud losses at $28.65 billion. That’s nearly 7 cents per every $100 in spending, representing significant losses across issuers, acquirers, and merchants.
Credit Card Fraud Tactics and COVID-19
So exactly how has credit card fraud morphed during the pandemic? As also reported in The Wall Street Journal, here’s a quick look at some trends and tactics:
- Fraudsters are generating random card numbers until they stumble upon legitimate accounts.
- More fraudulent purchases are being attempted with card numbers stolen in pre-pandemic hacks.
- Phishing attacks are on the rise during the pandemic. These include emails, texts and phone calls that attempt to trick customers into handing over their credit card credentials.
Special Tools to Combat Credit Card Fraud
In times of rapidly changing fraud patterns, banks and card issuers that use FICO’s fraud solutions are protected by numerous technologies that help detect more fraud, faster.
- FICO® Falcon® Platform is underpinned by contextual profiling technology that provides nano-profiling across any dimension of behavior, to find the real frauds and reduce false positives. For example, techniques pioneered by FICO such as behavioral sorted lists keep track of a customer’s favorite usage patterns. When a transaction occurs that is out of the normal pattern, it is flagged as potentially fraudulent.
Read the full post: Credit Card Fraud: It’s Still A Thing (And As Big As Ever)
How FICO Can Help You Control Fraud and Financial Crime
- Explore FICO’s solutions for fraud protection and financial crime compliance
Popular Posts

Has the Reporting of Rental Data to the Credit Reporting Agencies (CRAs) Increased?
FICO Score 10T includes rental data, but consumers can only experience the benefit of this to the extent that their rental data is reported to the CRAs
Read more
Average U.S. FICO® Score at 716, Indicating Improvement in Consumer Credit Behaviors Despite Pandemic
The FICO Score is a broad-based, independent standard measure of credit risk
Read more
FICO Statement on FHFA and FHA Updates to Credit Score Modernization
FICO supports FHFA’s announcement that the long-anticipated historical data for FICO® Score 10T will be released to the mortgage market.
Read moreTake the next step
Connect with FICO for answers to all your product and solution questions. Interested in becoming a business partner? Contact us to learn more. We look forward to hearing from you.

